
Canadian organizations and individuals are more connected than ever before and are using the Internet in novel ways. This is creating new and unique opportunities for cyber threat actors to exploit connections, cause disruptions and steal sensitive data.
This page provides resources from the Cyber Centre to help Canadian individuals and organizations understand the cyber threats facing Canada and learn how to better protect themselves.
About the National Cyber Threat Assessment (NCTA)
The NCTA is one of the Cyber Centre’s flagship cyber security reports. Its purpose is to help build Canada’s resilience to cyber threats. The NCTA explains the cyber threats facing Canada, describes the likelihood that these cyber threats will occur and outlines how they will evolve in the coming years. This forward-looking document is published every two years and is based on both classified and unclassified sources.
- National Cyber Threat Assessment 2025-2026
- National Cyber Threat Assessment 2023-2024
- National Cyber Threat Assessment 2020
- National Cyber Threat Assessment 2018
Introduction to the Cyber Threat Environment
Published alongside every iteration of the NCTA is an update to our Introduction to the Cyber Threat Environment. This reference document provides baseline information about the different types of cyber threats, as well as cyber threat actors, their motivations, their techniques and their tools in a Canadian context.
Advice and guidance
Many cyber threats can be mitigated through awareness and best practices in cyber security.
Below you’ll find tailored advice and guidance on the key topics identified in the NCTA.
Guidance on the threat of ransomware
“Ransomware is a persistent threat to Canadian organizations.”
Gains access
Threat actor finds a way into your network.
Takes control
Threat actor gains access of connected systems and services.
Impacts organization
Threat actor encrypts and copies your data, deletes connected backups, and demands a ransom.
Cybercrime continues to be the cyber threat activity most likely to affect Canadians and Canadian organizations. Due to its impact on an organization’s ability to function, ransomware is almost certainly the most disruptive form of cybercrime facing Canadians. Cybercriminals deploying ransomware have evolved in a growing and sophisticated cybercrime ecosystem and will continue to adapt to maximize profits. For comprehensive information on protecting your organization from ransomware, see the following publications, Ransomware playbook (ITSM.00.099), Ransomware: How to recover and get back on track, Ransomware: Don’t get locked out, and Ransomware: How to prevent and recover (ITSAP.00.099)
Top security actions for organizations
- Develop, test, and implement a backup plan for your organization that ensures your backups use ultra-resilient media, such as offline, air-gapped, or immutable, to prevent ransomware from impacting your ability to recover
- Develop, test, and implement an incident response and an information technology (IT) recovery plan
- Secure internet-exposed systems and applications by monitoring your networks continuously, running frequent updates, applying available patches, protecting data with encryption, running frequent vulnerability scans, and implementing measures to address scan results
- Implement network security zones to control and restrict access to specific systems and data, and restrict data communication flows to certain systems or zones
- Use secure administrative workstations to separate sensitive tasks, manage administrative privileges and accounts, and enforce multi-factor authentication (MFA) on accounts and devices wherever possible
- Move towards a zero trust security architecture to enhance the security of your environment and reduce your attack surface
- Deploy a host-based intrusion prevention system (HIPS) to protect your organization’s systems against both known and unknown malicious attacks
Additional resources
- Protect your organization from malware (ITSAP.00.057)
- Have you been a victim of cybercrime? (ITSAP.00.037)
- Spotting malicious email messages (ITSAP.00.100)
- Top measures to enhance cyber security for small and medium enterprises (ITSAP.10.035)
- Security considerations for consumers of managed services (ITSM.50.030)
- Protective Domain Name Service (ITSAP.40.019)
- Best practices for passphrases and passwords (ITSAP.30.032)
- Don’t take the bait: recognize and avoid phishing attacks (ITSAP.00.101)
- Baseline security controls for small and medium organizations
- How to protect your organization from malicious macros (ITSAP.00.200)
Guidance for critical infrastructure (CI)
“Critical infrastructure is increasingly at risk from cyber threat activity.”
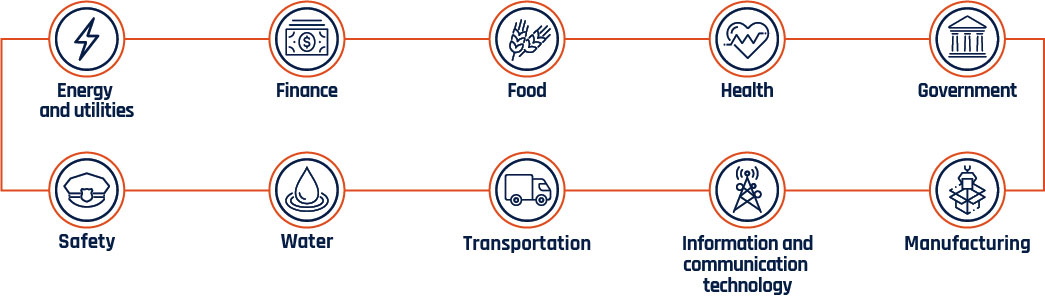
Long description - Critical infrastructure sectors
- Energy and utilities
- Finance
- Food
- Health
- Government
- Safety
- Water
- Transportation
- Information and communication technology
- Manufacturing
Cybercriminals exploit CI because downtime can be harmful to their industrial processes and the customers they serve. State-sponsored actors target CI to collect information through espionage, to pre-position in case of future hostilities, and as a form of power projection and intimidation. However, we assess that state-sponsored cyber threat actors will very likely refrain from intentionally disrupting or destroying Canadian CI in the absence of direct hostilities. For more information, see Security considerations for Critical Infrastructure (ITSAP.10.100).
Top security actions for CI organizations
- Isolate CI components and services from the internet when under imminent threat, such as a ransomware incident or denial of service attack
- Use secure administrative workstations to separate sensitive tasks and manage administrative privileges and accounts
- Implement network security zones to control and restrict access and data communication flows to certain components and users
- Test manual controls to ensure critical functions remain operable if your network is unavailable
- Identify, separate, and monitor your information technology (IT) and operational technology (OT) networks
- Test OT, including industrial control systems (ICS), as part of your incident response plan to ensure critical functions remain operational during an outage or cyber incident
- Secure your supply chain by implementing a multistep review process that includes validation and verification (V&V) of processes, as well as a risk assessment of your vendor’s cyber security operations
Additional resources
- Network security zoning - Design considerations for placement of services within zones (ITSG-38)
- Cyber security hygiene best practices for your organization (ITSAP.10.102)
- Top 10 IT security actions to protect Internet connected networks and information (ITSM.10.089)
- Protective Domain Name Service (ITSAP.40.019)
- Internet of Things (IoT) Security (ITSAP.00.012)
- Secure your accounts and devices with multi-factor authentication (ITSAP.30.030)
- Security in layers with Multi-Factor Authentication
- Using encryption to keep your sensitive data secure (ITSAP.40.016)
- Identity, Credential, and Access Management (ICAM) (ITSAP.30.018)
- Protect information at the enterprise level (ITSAP.10.097)
Guidance on the threat of state-sponsored actors
“State-sponsored cyber threat activity is impacting Canadians.”
China
Russia
North Korea
Iran
We assess that the state-sponsored cyber programs of China, Russia, Iran, and North Korea pose the greatest strategic cyber threats to Canada. State-sponsored cyber threat activity against Canada is a constant, ongoing threat that is often a subset of larger, global campaigns undertaken by these states. State actors can target diaspora populations and activists in Canada, Canadian organizations and their intellectual property for espionage, and even Canadian individuals and organizations for financial gain. For more information on assessing, understanding and mitigating the risks posed by state-sponsored threat actors, see State-sponsored espionage and threats to critical infrastructure.
Top security actions for organizations
- Review critical network services and internet-exposed system logs and isolate web-facing applications
- Enhance insider threat monitoring and implement a “two-person” rule when performing critical administrative functions to guard against social engineering tactics by highly sophisticated threat actors
- Deploy perimeter defences and preventative security tools, including a host-based intrusion prevention system (HIPS) to protect your organization’s systems against both known and unknown malicious attacks
- Enforce multi-factor authentication (MFA) for all users to your organization’s network, manage and control administrative privileges, implement the principle of least privilege to access rights across your organization, and monitor your networks for data exfiltration
- Adhere to your organization’s patch management process to assess, test, manage changes, and apply patches as soon as they are released
Additional resources
- Using encryption to keep your sensitive data secure (ITSAP.40.016)
- Protect your organization from malware (ITSAP.00.057)
- Have you been a victim of cybercrime? (ITSAP.00.037)
- Spotting malicious email messages (ITSAP.00.100)
- Supply chain security for small and medium-sized organizations (ITSAP.00.070)
- Top 10 IT security action items: No. 10 Implement application allow lists (ITSM.10.095)
- Implementation guidance: email domain protection (ITSP.40.065)
- Don’t take the bait: recognize and avoid phishing attacks (ITSAP.00.101)
- What is voice phishing (vishing)? (ITSAP.00.102)
Guidance on the threat of misinformation, disinformation and malinformation (MDM)
“Cyber threat actors are attempting to influence Canadians, degrading trust in online spaces.”
We have observed cyber threat actors’ use of misinformation, disinformation, and malinformation (MDM) evolve over the past two years. Machine-learning enabled technologies are making fake content easier to manufacture and harder to detect. Further, nation states are increasingly willing and able to use MDM to advance their geopolitical interests. We assess that Canadians’ exposure to MDM will almost certainly increase over the next two years. For more information on MDM, see How to identify misinformation, disinformation, and malinformation (MDM) (ITSAP.00.300).
Top security actions for organizations
- Implement multi-factor authentication (MFA) wherever possible to secure your devices and accounts (including your social media accounts)
- Research the various mobile device deployment models and weight the pros and cons to ensure you select the most secure option for your organization
- Consider the security concerns associated when using social media in your organization
- Develop and manage your website securely by applying principles like segregation and redundancy to your architecture, implementing strong authentication factors, and robust input validation
- Set up social media and web monitoring, as well as alerting services for identifying and tracking fake news related to your brand and organizations
Additional resources
- Use of personal social media in the workplace (ITSAP.00.066)
- Mobile devices guidance for high profile travellers (ITSAP.00.088)
- Digital footprint (ITSAP.00.133)
- Security considerations when developing and managing your website (ITSAP.60.005)
- Loss of control of social media channels
- Social media account impersonation
- Using your mobile device securely (ITSAP.00.001)
- Have you been hacked? (ITSAP.00.015)
- Protecting yourself from identity theft online (ITSAP.00.033)
- Spotting malicious email messages (ITSAP.00.100)
Guidance on the threat of disruptive technologies
“Disruptive technologies bring new opportunities and new threats.”
Digital assets, such as cryptocurrencies and decentralized finance, are both targets and tools for cyber threat actors to enable malicious cyber threat activity. Machine learning has become commonplace in consumer services and data analysis, but cyber threat actors can deceive and exploit this technology. Quantum computing has the potential to threaten our current systems of maintaining trust and confidentiality online. Encrypted information stolen by threat actors today can be held and decrypted when quantum computers become available.
Top security actions for organizations
- Assess and understand the risks associated with the adoption of these new technologies
- Leverage capabilities such as artificial intelligence, advanced analytics, and machine learning to rapidly identify emerging trends and implement risk controls to protect your organization
- Implement operations security (OPSEC) and verification actions when using machine learning applications
- Track findings from trusted sources (e.g. government publications, industry experts) on quantum cryptography developments
- Confirm whether your vendors use standardized, validated cryptography (e.g. validated modules under the Cryptographic Module Validation Program) in current and future agile products
- Exercise caution when considering the use of cryptocurrency and understand the risks of fluctuating value and lack of regulatory governance
Additional resources
Report a cyber incident
Reporting a cyber incident helps the Cyber Centre keep Canada and Canadians safe online. Your information will enable us to provide cyber security advice, guidance and services.
Get Cyber Safe
Get Cyber Safe is a national public awareness campaign created to inform Canadians about cyber security and the simple steps they can take to protect themselves online.
