Overview
On February 28, 2026, the United States (U.S.) and the State of Israel (Israel) launched military strikes against the Islamic Republic of Iran (Iran) to eliminate threats from the Iranian regime.Footnote 1 Iran retaliated with military strikes against Israel and U.S. military bases across the Middle East.Footnote 2
On February 28, 2026, the Government of Canada released a statement supporting the United States acting to prevent Iran from obtaining a nuclear weapon and to prevent its regime from further threatening international peace and security.Footnote 3
Iran will very likely use its cyber program to respond to the joint U.S. and Israel combat operations against Iran. Possible responses by Iranian cyber threat actors include:
- Cyber attacks against critical infrastructure;
- Cyber-enabled information operations;
- Online harassment of military personnel; and
- Harassment and repression of diaspora and activist communities.
Canadian critical infrastructure operators and other possible targeted entities should remain vigilant to threats posed by cyber actors aligned with Iranian interests.
Iran uses cyber program to retaliate, achieve geopolitical goals
- Iranian state-sponsored cyber threat actors conduct disruptive cyber-enabled information operations to further Iran’s geopolitical objectives and the regime’s interests. Iran has developed a network of hacktivist personas and social media channels to intimidate Iran’s opponents and shape public opinion.Footnote 4
- Iranian state-sponsored cyber threat actors opportunistically target poorly secured critical infrastructure (CI) networks and internet-connected devices around the world, including those associated with the water and energy sectors.Footnote 5 Iranian cyber threat actors have performed denial of services attacks, attempted to manipulate industrial control systems, and accessed networks to encrypt, wipe, and leak data.Footnote 6
- Pro-Iran hacktivists conduct cyber threat activity against Iran’s rivals, but often overstate their impact. In response to the U.S. airstrikes on Iranian nuclear sites in 2025, pro-Iran hacktivist groups claimed to have conducted distributed denial-of-service (DDoS) attacks against websites associated with the U.S. military, U.S. defence companies and U.S. financial institutions.Footnote 7 Pro-Iran hacktivists will likely view Canada as a target for low-sophistication disruptive cyber activity due to Canada’s public support of the US/Israel military activity.
- Iranian state-sponsored cyber threat actors likely conduct cyber espionage against individuals in Canada that the Iranian regime considers a threat, such as political activists, journalists, and human rights advocates.Footnote 4 We assess that Iranian cyber threat actors will likely target opponents abroad, especially those advocating for regime change in Iran.Footnote 8
Characteristics of Iranian cyber threat activity
Compelling social engineering
Iranian cyber threat groups are particularly sophisticated in combining social engineering with spear phishing, using these efforts to target public officials and gain access to government networks and private sector organizations globally.Footnote 9
Iranian social engineering efforts focus on using professional interactions on social media platforms to gain information about organizations related to Iran’s political, economic and military interests, particularly in the aerospace, energy, defence, security, and telecommunications sectors.Footnote 9
Exploiting known vulnerabilities
Iranian cyber threat actors exploit known vulnerabilities to gain initial access to systems, and then leverage this access for follow on operations such as data exfiltration or encryption, ransomware, and extortion.Footnote 10
Iranian cyber threat actors opportunistically identify targets using publicly available scanning tools to search for internet-exposed systems with vulnerable configurations, for example devices using default or weak passwords and without multi-factor authentication.Footnote 11
Disruptive and destructive cyber attacks
Iranian cyber threat actors typically conduct DDoS attacks and website / device defacements to temporarily disrupt target networks. They also deploy ransomware and destructive wiper malware and conduct hack-and-leak operations against compromised targets.Footnote 12
Useful resources
Refer to the following online resources for more information and useful advice and guidance.
Reports and advisories
- Canada’s threat assessments
- Advisories and partner publications
Advice and guidance
- Cyber Security Readiness Goals (CRGs): Securing Our Most Critical Systems
- Cross-Sector Cyber Security Readiness Goals Toolkit
- Security considerations for critical infrastructure
- Top 10 IT security actions to protect Internet connected networks and information
- Top 10 IT security action items: No.2 patch operating systems and applications
- Protect your organization from malware
- Security considerations for your website
- Security considerations for edge devices
- Defending against distributed denial of service (DDoS) attacks
- Secure your accounts and devices with multi-factor authentication
- Don't take the bait: Recognize and avoid phishing attacks
- What to do when your organization has been compromised by a cyber attack
About this document
Contact
For follow-up questions or issues, contact the Cyber Centre at contact@cyber.gc.ca.
Assessment base and methodology
The key judgements in this assessment rely on reporting from multiples sources, both classified and unclassified. The judgements are based on the Canadian Centre for Cyber Security (Cyber Centre)’s knowledge and expertise in cyber security. Defending the Government of Canada’s information systems provides the Cyber Centre with a unique perspective to observe trends in the cyber threat environment, which also informs our assessments. CSE’s foreign intelligence mandate provides us with valuable insight into adversary behavior in cyberspace. While we must always protect classified sources and methods, we provide the reader with as much justification as possible for our judgements.
Our key judgements are based on an analytical process that includes evaluating the quality of available information, exploring alternative explanations, mitigating biases and using probabilistic language. We use terms such as “we assess” or “we judge” to convey an analytic assessment. We use qualifiers such as “possibly”, “likely”, and “very likely” to convey probability.
The contents of this document are based on information available as of February 28, 2026.
Estimative language
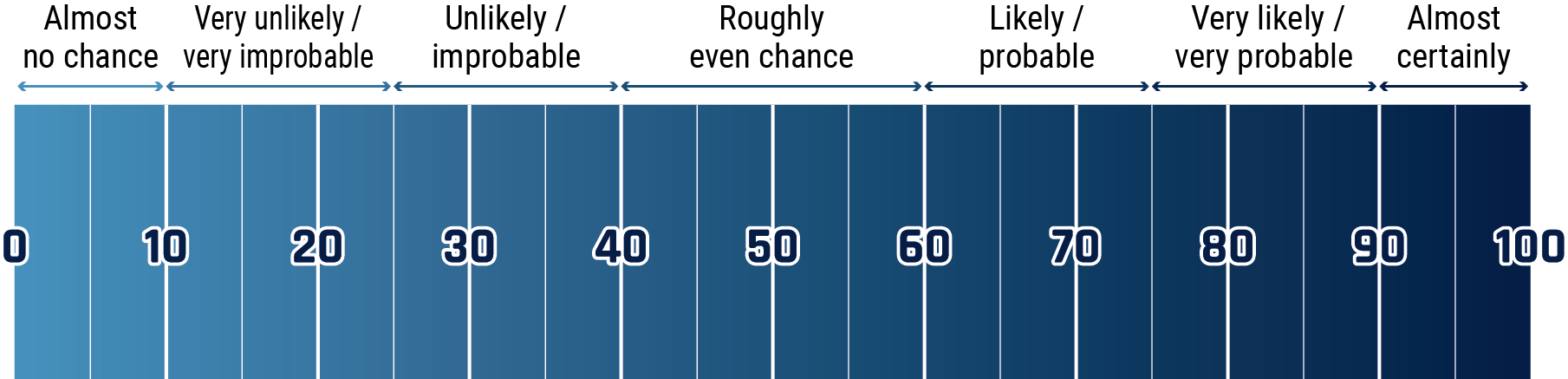
Long description - Estimative language chart
- 1 to 9% Almost no chance
- 10 to 24% Very unlikely/Very Improbable
- 25 to 39% Unlikely/Improbable
- 40 to 59% Roughly even chance
- 60 to 74% Likely/probably
- 75 to 89% Very likely/very probable
- 90 to 100% Almost certainly