The Canadian Centre for Cyber Security (Cyber Centre) is actively tracking a campaign exploiting blockchain technology to covertly host and distribute malware. This campaign leverages a technique known as EtherHiding.
The Cyber Centre has compiled a detailed analysis derived from a recent investigation to help defenders combat attacks leveraging this technique. This analysis examines the evolution and use of the EtherHiding technique and provides an in-depth characterization of the threat actor’s techniques, along with critical mitigation and detection guidance.
Executive summary
This technical article aims to raise awareness and describe some of the tactics, techniques, and procedures (TTPs) associated with EtherHiding. The Cyber Centre’s preliminary findings highlight that, in the analyzed incident, the threat actor inserted a malicious one-liner JavaScript downloader inside a configuration file for the Tailwind CSS framework (tailwind.config.js).
The downloaded JavaScript payload is a highly advanced backdoor designed for a covert operation, as it operates within the Node.js runtime environment that is embedded in Visual Studio Code (VS Code) or Cursor AI (a modified version of VS Code). It is designed to infect developer machines, perform file or directory theft, and execute command from a command-and-control server (C2). The subsequent analysis of this backdoor module provided valuable insights into the extent of the compromise as well as the threat actor’s intentions and activities.
An incident overview
Disclaimer: Although it is unknown how the threat actor was able to push the file, this technical analysis focuses on how the threat actor was able to achieve remote code execution, maintain persistence, leverage C2 techniques and exfiltrate data.
While working on an artificial intelligence (AI) source project that used the Node.js Tailwind CSS framework, a developer observed an unknown commit made to their private internal GitHub repository. That commit modified their tailwind.config.js file in plain sight. Padded with over a thousand whitespace characters, the file blended seamlessly into the developer’s workspace – making it especially difficult to spot during routine code reviews. Technical support was sought from the Cyber Centre to assist with threat analysis and identification.
The malicious code is designed to take advantage of the Node.js ecosystem, which is commonly used by developers to build and test applications. When a developer interacts with the repository, the hidden payload is triggered within the environment without their knowledge.
Figure 1: Attack path depicting how the threat actor gained access and moved through the environment
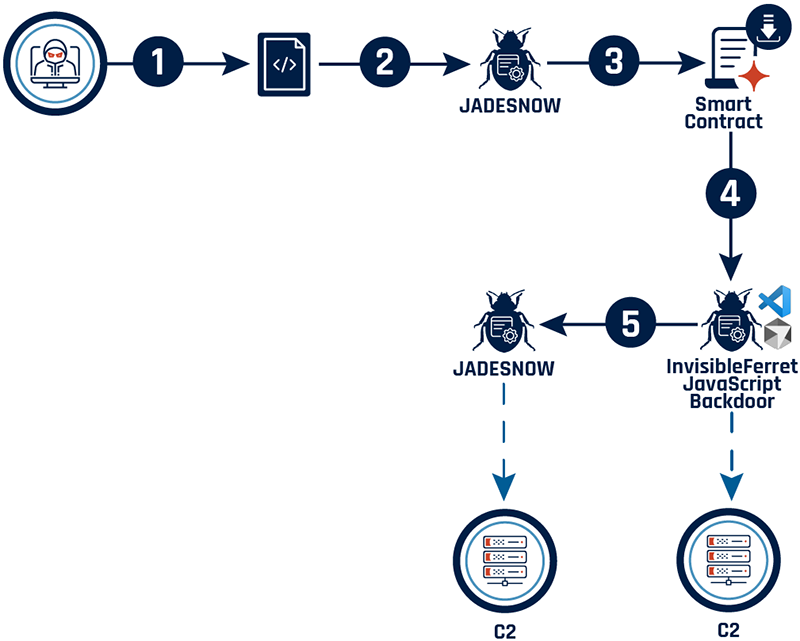
Long description - Attack path depicting how the threat actor gained access and moved through the environment
The figure depicts a multi-stage cyber attack flowchart. It starts with the execution of a malicious JavaScript file that retrieves transaction hashes from cryptocurrency platforms. This triggers a chain of events involving multiple downloaders and a JavaScript backdoor (InvisibleFerret) to execute malicious payloads and enable unauthorized access.
Analysis of the incident
Disclaimer: To enhance source code readability, content may be updated by adding comments or renaming functions and variables.
mitre att&CK techniques observed during analysis
The information below is based on the attack path outlined in figure 1.
Observation 1
- Main technique: Command and scripting interpreter: JavaScript (T1059.007)
- Additional techniques: Masquerading (T1036)
- Stage capabilities: Upload malware (T1608.001)
Observation 2
Observation 3
- Main technique: Application layer protocol: Web protocols (T1071.001)
- Additional techniques: Application layer protocol: DNS (T1071.004) and System location discovery (T1614)
Observation 4
- Main technique: Exfiltration over C2 channel (T1041)
Observation 1
Observed tactics: Execution (TA0002); Defense evasion (TA0005); Resource development (TA0042)
Observed techniques: Command and scripting interpreter: JavaScript (T1059.007); Masquerading (T1036); Stage capabilities: Upload malware (T1608.001)
Once triggered, the malware runs custom JavaScript routines that decrypt and launch additional payloads. The attack is multi-staged and dynamic.
Stage 1
The tailwind.config.js file loads a jadesnow downloader that requests a transaction hash from hardcoded wallet addresses on the tron or Aptos blockchains.Footnote 1
Figure 2: Flow diagram illustrating how the script requests a transaction hash
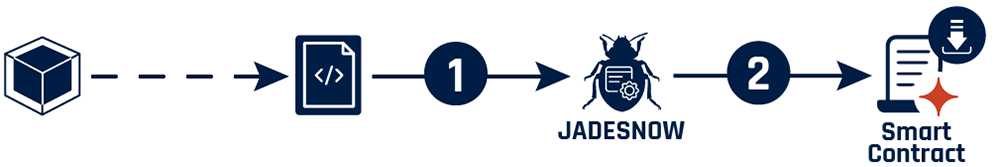
Long description - Flow diagram illustrating how the script requests a transaction hash
The figure illustrates the initial stages of a cyber attack, starting with the execution of a malicious JavaScript file (tailwind.config.js) within a Node.js environment. This script triggers the jadesnow Downloader1, which retrieves a transaction hash from cryptocurrency platforms.
Stage 2
Using the transaction hash, the jadesnow downloader fetches a payload from the Binance Smart Chain (BSC) via a JSON RPC post request. The payload is XOR-decrypted using a hardcoded key and executed as JavaScript.
Figure 3: Flow diagram illustrating how the payload is XOR-decrypted
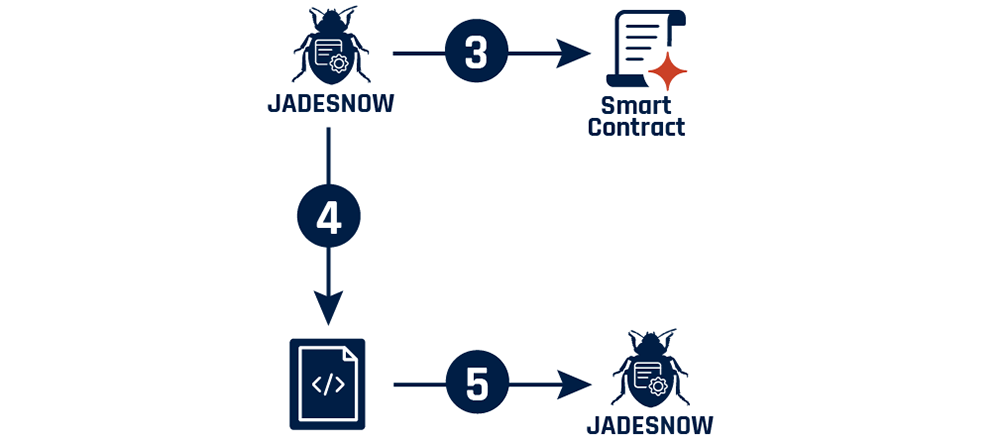
Long description - Flow diagram illustrating how the payload is XOR-decrypted
The figure depicts a cyber attack segment involving two malicious downloaders. The "jadesnow Downloader1" downloads a payload from Binance (step 3) and decrypts the payload using XOR (step 4) to produce a JavaScript file (payload1.js). The decrypted file is then executed (step 5), triggering "jadesnow Downloader2" to continue the attack chain.
Stage 3
The decrypted payload is another jadesnow downloader, repeating the blockchain fetch-and-decrypt process with new wallet combinations and a hardcoded XOR key. The payload is a loader for the InvisibleFerret.JavaScript backdoor.Footnote 2
Figure 4: How the decrypted payload repeats the process using new wallet combinations
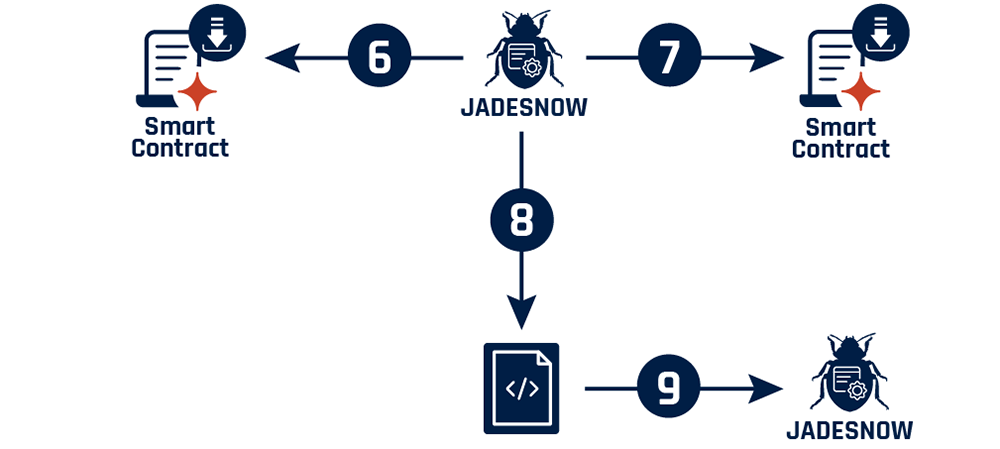
Long description - Flow diagram illustrating how the payload is XOR-decrypted
The figure depicts how the "jadesnow Downloader2" retrieves a transaction hash from the TRON and Aptos cryptocurrency platforms. Using that transaction hash, it downloads a payload from Binance which is decrypted using XOR to produce a JavaScript file (payload2.js). It is then executed to trigger "jadesnow Downloader1" and continue the attack sequence.
Stage 4
The last payload is another jadesnow downloader that is XOR-decrypted using a static key. This variant of the malware checks for a kill switch (process.env.jsbot) to terminate itself if detected, attempts to deploy Python (python.zip, python.7z, 7zr.exe), and runs scripts (boot, client) for further compromise.
Figure 5: XOR decryption key
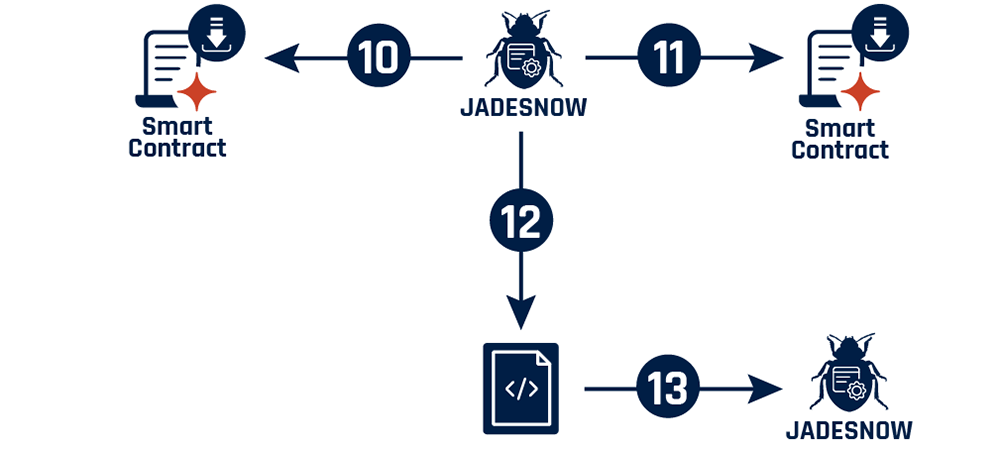
Long description - Figure 5: XOR decryption key
The figure depicts how the "jadesnow Downloader1" retrieves a transaction hash from the TRON and APTOS cryptocurrency platforms. Using that transaction hash, it downloads a payload from Binance which is decrypted using XOR to produce a JavaScript file (payload3.js). It is then executed to trigger "jadesnow Downloader3" and continue the attack sequence.
Observation 2
Observed tactics: Privilege escalation (TA0004); Persistence (TA0003)
Observed technique: Event triggered execution: Component object model hijacking (T1546.015)
InvisibleFerret.JavaScript injects itself into the telemetry files of VS Code and Cursor AI to reconfigure files like index.js in the editor’s internal modules. The injected code includes custom session labelling, such as [5-74-<date>]<hostname>$<username>.
It maintains persistent communication with its operators using both HTTP POST and socket.io connections while it waits for commands and will attempt to reconnect every five seconds if the connection is dropped.
Since this module is responsible for generating unique machine IDs, hijacking it allows the malware to:
- track users across sessions and installations
- leak identifying information
- maintain persistent access
Paths for the injected file varies by operating system (OS):
- Windows: %localappdata%\Programs\Microsoft VS Code\resources\app\node_modules\@vscode\deviceid\dist\index.js
- MacOS: /Applications/Visual Studio Code.app/Contents/Resources/app/node_modules/@vscode/deviceid/dist/index.js
- Linux: /usr/share/code/resources/app/node_modules/@vscode/deviceid/dist/index.js
Observation 3
Observed tactics: Command and control (TA0011); Discovery (TA0007)
Observed techniques: Application layer protocol: Web protocols (T1071.001); Application layer protocol: DNS (T1071.004); System location discovery (T1614)
Communication with the attacker’s infrastructure is handled specifically via HTTP POST requests to hardcoded internet protocol (IP) addresses and uniform resource identifiers (URIs). Various C2 servers and endpoints include a numerical value of 5-74 in the uniform resource locator (URL) which corresponds to a malware or campaign version number defined in the JavaScript program.
The malware fetches external internet protocol (IP) information to determine the geographical location of the victim, helping attackers profile the infected environment and tailor their operations. It also supports a wide range of other commands, as outlined below.
Supported commands with descriptions and techniques
- cd: changes the current location to the target directory
- ss_info: returns information about the running Node.js application: version, session, operating system, and path
- ss_ip: gets the external IP address information from ip-api[.]com/json
- ss_upf: uploads a file
- ss_upd: uploads a directory
- ss_dir: changes the current location to the module directory
- ss_fcd: changes the current location to the target directory
- ss_inz: injects JavaScript code in VSCode
- ss_eval: executes JavaScript code using eval
The commands above enable a threat actor to conduct data collection activities (Tactic: Collection (TA0009) – Data from Local System (T1005)) and run arbitrary code on affected systems.
Observation 4
Observed tactic: Exfiltration (TA0010)
Observed technique: Exfiltration over C2 channel (T1041)
Robust, recursive routines are used to upload a single file or an entire directory to attacker-controlled servers. The malware then leverages Node.js modules like Axios and form data to craft HTTP POST requests with multipart/form-data, ensuring compatibility with web servers and stealth in transit.
The malware’s recursive upload function (recursiveHttpUpload) walks through directories, collecting file paths and uploading each file individually. Success and failure counts are tracked, and status messages are sent back to the C2 via socket.io events. The exfiltration is not limited to files, as entire directory trees can be sent, enabling attackers to siphon off large volumes of source code, configuration files or sensitive data in one go.
Indicators of compromise and recommendations
Indicators of compromise (IoCs) were distributed through alerts and communications by the Canadian Cyber Security Incident Response Team (CSIRT). This ensured that partners across all sectors had the information they needed to act decisively.
For up-to-date information on alerts and advisories or cyber security guidance, please contact the Cyber Centre.
Malicious JavaScript configuration
- tailwind.config.js
- SHA256: d043f264ff5216fa724cad2d35ba4d895c43e295df72be6d46c07a3a46cfbd62
Payloads
- payload2.js (InvisibleFerret.Javascript)
- SHA256: 7237310e076459d2fce2f531941b5920e451f390a8b8e633787b62b68b1315d5
- boot-decoded-2.js
- SHA256: 91822e59bd642f8e6f321011d0fb45b8a5f0854547ea898dead5d5af1db3ed9b
C2 URL
- /verify-human/5-74
C2 URL for upload endpoint
- /u/f/
C2 IPs
- 166.88.4[.]2
- 23.27.202[.]27
- 23.27.202[.]143
- 136.0.9[.]8
C2 port
- 27017
Cyber Centre tools and services
No single tool, service or turnkey solution can reconstruct an incident, trace an attacker’s path or validate a threat on its own. A holistic approach using multiple perspectives is required to conduct a thorough investigation. As such, the Cyber Centre relies on multiple layered telemetry sources to detect threats and protect monitored assets.
AssemblyLine was used to enable triage at scale, processing hundreds of thousands of files per day. In response to this incident, the Cyber Centre also created YARA rules to help with the detection of malicious files related to the threat actor’s activity. Additional YARA rules will be released periodically after an evaluation period to ensure accuracy.
The YARA rule below enables a detection of similar payloads extracted from the compromised host.
Figure 6: YARA rule for jadesnow obfuscated downloader
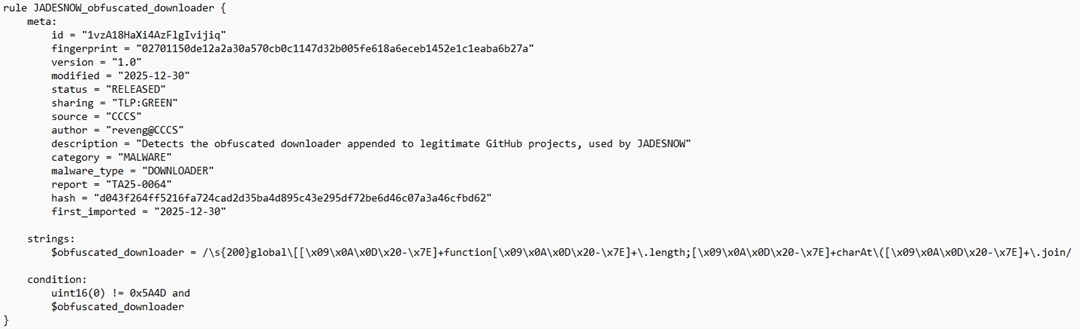
Long description - Figure 6: YARA rule for jadesnow obfuscated downloader
This YARA rule specifically targets malware associated with the jadesnow actor group. It uses a combination of metadata, including a unique identifier, fingerprint, version, and description, along with a specific string pattern and condition to identify the presence of the obfuscated downloader in files. The condition checks for a specific hexadecimal value and the presence of a defined obfuscated string pattern to flag potential threats.
Code rule jadesnow_obfuscated_downloader { meta: id = "1vzA18HaXi4AzFlgIvijiq" fingerprint = "02701150de12a2a30a570cb0c1147d32b005fe618a6eceb1452e1c1eaba6b27a" version = "1.0" modified = "2025-12-30" status = "released" sharing = "TLP:GREEN" source = "CCCS" author = "reveng@CCCS" description = "Detects the obfuscated downloader appended to legitimate GitHub projects, used by jadesnow" category = "malware" malware_type = "downloader" report = "TA25-0064" hash = "d043f264ff5216fa724cad2d35ba4d895c43e295df72be6d46c07a3a46cfbd62" first_imported = "2025-12-30" strings: $obfuscated_downloader = /\s{200}global\[[\x09\x0A\x0D\x20-\x7E]+function[\x09\x0A\x0D\x20-\x7E]+\.length;[\x09\x0A\x0D\x20-\x7E]+charAt\([\x09\x0A\x0D\x20-\x7E]+\.join/ condition: uint16(0) != 0x5A4D and $obfuscated_downloader }
Acknowledgments
As a part of the Communications Security Establishment Canada (CSE), the Cyber Centre is a proud member of the Five Eyes, the world’s longest-standing and closest intelligence-sharing alliance. Sharing IoCs and TTPs with the cyber community and Five Eyes partners has been instrumental since the EtherHiding campaign was first discovered, and ongoing analytical exchanges have maximized the value of collected data.
Further collaboration with organizations such as Mandiant has enabled the exchange of detailed malware analysis and technical findings, strengthening collective defences.
Disclaimer: The Cyber Centre disclaims all liability for any loss, damage, or costs arising from the use of or reliance on the information within this article. Readers are solely responsible for verifying the accuracy and applicability of any information before acting on it.